All Security Culture
- How we can get ‘more of everything’ for the cybersecurity workforceWith a need for 1.5 million more trained professionals in coming years, the federal government, universities, and companies are teaming up to solve the problem.
 Why does our privacy really matter?Philosophy professor Michael Lynch says that privacy violations erode individuals' rights to autonomously make their own decisions and exercise individual power.
Why does our privacy really matter?Philosophy professor Michael Lynch says that privacy violations erode individuals' rights to autonomously make their own decisions and exercise individual power.- How secure is your data? Take our quiz and find out
Do you use Tor browser, two-factor authentication, or a VPN? Do you know what those things are? With data breaches commonplace and digital surveillance on the rise, there's no better time to find out if your own private information is shielded from prying eyes. Take our quiz designed in partnership with the Mozilla Foundation and the Center for Democracy and Technology to find out how to secure yourself against a growing number of threats online.
 US CIO Tony Scott on fixing cybersecurity's talent gapAt a Passcode event Tuesday, the US chief information officer said the federal government wants candidates who know languages, biology, and anthropology to fill cybersecurity roles – and one of its most important hires, the new chief information security officer, will be announced within 30 days.
US CIO Tony Scott on fixing cybersecurity's talent gapAt a Passcode event Tuesday, the US chief information officer said the federal government wants candidates who know languages, biology, and anthropology to fill cybersecurity roles – and one of its most important hires, the new chief information security officer, will be announced within 30 days. Watch live: Workforce 2.0, cultivating cybersecurity professionalsAround the world, an estimated 1 million cybersecurity jobs are currently unfilled. Join a panel discussion on how to cultivate cybersecurity talent on Tuesday, April 12.
Watch live: Workforce 2.0, cultivating cybersecurity professionalsAround the world, an estimated 1 million cybersecurity jobs are currently unfilled. Join a panel discussion on how to cultivate cybersecurity talent on Tuesday, April 12. Tor aims to grow amid national debate over digital privacyThe Tor Project's new executive director Shari Steele is on a mission to change the image of the group's anonymous browser and make its 'clunky and hard to use' technology more user-friendly.
Tor aims to grow amid national debate over digital privacyThe Tor Project's new executive director Shari Steele is on a mission to change the image of the group's anonymous browser and make its 'clunky and hard to use' technology more user-friendly. Will recycling the San Bernardino iPhone hack put consumers at risk?Now that the FBI has unlocked the San Bernardino iPhone, there's a new public debate over how to responsibly disclose vulnerabilities the government finds. Security pros say that once a technical flaw is announced, it must be patched quickly – but law enforcement may be able to reuse them in future cases.
Will recycling the San Bernardino iPhone hack put consumers at risk?Now that the FBI has unlocked the San Bernardino iPhone, there's a new public debate over how to responsibly disclose vulnerabilities the government finds. Security pros say that once a technical flaw is announced, it must be patched quickly – but law enforcement may be able to reuse them in future cases. Opinion: Hacker or hacktivist? In data security, it doesn't really matterMuch of the cybersecurity field is too focused on attributing hacks. Instead, companies trying to defend their data should do more to protect their data from any attacker.
Opinion: Hacker or hacktivist? In data security, it doesn't really matterMuch of the cybersecurity field is too focused on attributing hacks. Instead, companies trying to defend their data should do more to protect their data from any attacker. Solutions emerge at highly anticipated SXSW harassment summitThis year's South by Southwest Interactive festival in Austin dedicated a series of panel discussions on how to combat the growing problem of online abuse in social media and gaming.
Solutions emerge at highly anticipated SXSW harassment summitThis year's South by Southwest Interactive festival in Austin dedicated a series of panel discussions on how to combat the growing problem of online abuse in social media and gaming. Hackers in trainingStudents from two of the world’s top universities raced to conquer a range of cybersecurity challenges at the Massachusetts Institute of Technology.
Hackers in trainingStudents from two of the world’s top universities raced to conquer a range of cybersecurity challenges at the Massachusetts Institute of Technology. Opinion: Why constantly changing your passwords may not improve securityRequiring frequent password changes in the name of security might not be as effective as previously thought, especially if people are just adding another character onto an old password.
Opinion: Why constantly changing your passwords may not improve securityRequiring frequent password changes in the name of security might not be as effective as previously thought, especially if people are just adding another character onto an old password. Sophisticated banking malware targets Android usersResearchers have discovered malicious software targeting online banking customers that use Android smartphones and tablets, the latest indication of a surge in attacks against the platform.
Sophisticated banking malware targets Android usersResearchers have discovered malicious software targeting online banking customers that use Android smartphones and tablets, the latest indication of a surge in attacks against the platform. In nod to Silicon Valley, Pentagon opens door to hackersThe Department of Defense announced it will launch the federal government's first bug bounty program for vetted hackers to search its systems for vulnerabilities.
In nod to Silicon Valley, Pentagon opens door to hackersThe Department of Defense announced it will launch the federal government's first bug bounty program for vetted hackers to search its systems for vulnerabilities. WordPress joins movement toward HTTPS encryptionPopular blogging platform WordPress is the latest in a growing number of sites that are enabling website encryption to protect their users.
WordPress joins movement toward HTTPS encryptionPopular blogging platform WordPress is the latest in a growing number of sites that are enabling website encryption to protect their users. Survey: Consumers reject companies that don't protect privacyAt Thursday’s Data Privacy Day event in Washington, Passcode joined privacy and security experts to explore US consumers' evolving attitudes about digital privacy.
Survey: Consumers reject companies that don't protect privacyAt Thursday’s Data Privacy Day event in Washington, Passcode joined privacy and security experts to explore US consumers' evolving attitudes about digital privacy. Podcast: Intel's Chris Young on why the US needs a Cyber National GuardChris Young of Intel Security and Chris Wysopal of Veracode join The Cybersecurity Podcast to talk about hacker culture, threats from the Internet of Things, and the suspected cyberattack on the Ukrainian power grid.
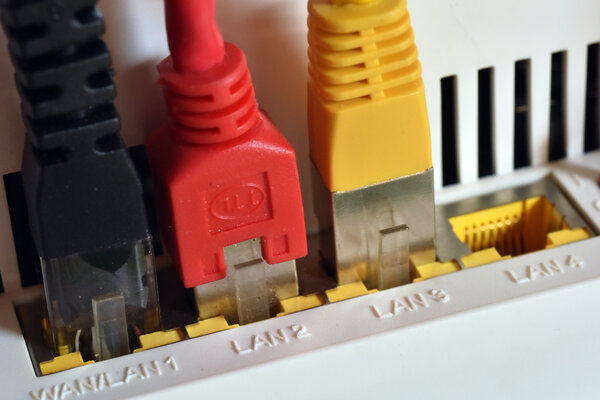
Podcast: Intel's Chris Young on why the US needs a Cyber National GuardChris Young of Intel Security and Chris Wysopal of Veracode join The Cybersecurity Podcast to talk about hacker culture, threats from the Internet of Things, and the suspected cyberattack on the Ukrainian power grid.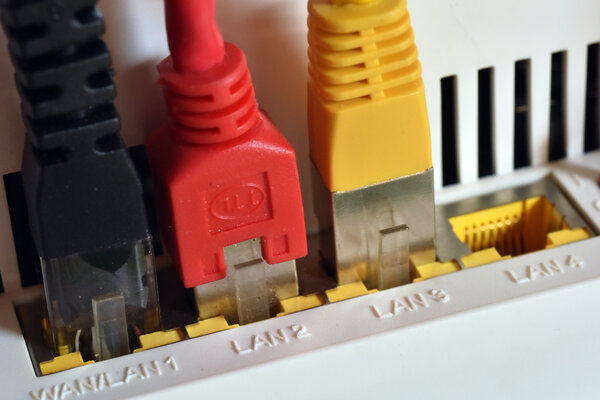 Your Internet router is a security risk. Here's whyNot only are many home and small office routers sold with security vulnerabilities, the devices are often difficult for users to update and easy for hackers to penetrate.
Your Internet router is a security risk. Here's whyNot only are many home and small office routers sold with security vulnerabilities, the devices are often difficult for users to update and easy for hackers to penetrate. The ad blockers debate: What's at stake for consumers and Web publishersBig media companies have ramped up efforts to fight the growing use of technology designed to block online ads. Here's what you need to know about why ad blockers are on the rise, and why many publishers hate them.
The ad blockers debate: What's at stake for consumers and Web publishersBig media companies have ramped up efforts to fight the growing use of technology designed to block online ads. Here's what you need to know about why ad blockers are on the rise, and why many publishers hate them. Facebook's balancing act between trust and securityThe Paris attacks highlight the delicate dance for Facebook. But Chief Security Officer Alex Stamos says it's vital for the social network to defend users' privacy – and foster trust among its online community – in the face of growing pressure from governments to reveal more information about the platform's 1.5 billion users.
Facebook's balancing act between trust and securityThe Paris attacks highlight the delicate dance for Facebook. But Chief Security Officer Alex Stamos says it's vital for the social network to defend users' privacy – and foster trust among its online community – in the face of growing pressure from governments to reveal more information about the platform's 1.5 billion users. Want to stop apps from sharing your data? There’s an app for that, tooNortheastern University researchers launched an app called ReCon to track and limit the personal information that's collected and shared by other smartphone apps.
Want to stop apps from sharing your data? There’s an app for that, tooNortheastern University researchers launched an app called ReCon to track and limit the personal information that's collected and shared by other smartphone apps.